Did you know a traditional sign-in process consumes an average of 5 minutes per visitor? Multiply that by the number of daily visitors, and you’ll find a significant chunk of valuable time wasted.
A visitor management software can effectively mitigate risks associated with visitors onsite and ensure site security by providing a streamlined and organized system for tracking and monitoring visitor activity through visitor profiles, a digital record of all visitors, real-time alerts and notifications, and comprehensive visitor data analytics and reporting capabilities.
In light of the growing complexity of business settings and the ever-evolving landscape of security threats, it is imperative to employ strategies to optimize workplace security protocols, with one prominent solution being the implementation of a visitor management system. With the rising recognition of such systems, companies around the globe are transitioning from traditional paper and pen sign-in sheets to advanced digital visitor management. By comprehending the multiple risks associated with the different types of visitors on site and key components in a visitor management system capable of mitigating these risks, businesses can determine what to look for when opting for visitor management software. Visitor management software streamlines this process, reducing check-in time to mere seconds. Businesses can save up to 30% of their operational costs by investing in a robust visitor management system, from reducing paperwork expenses to minimizing the need for additional security personnel.
Major Risks Associated With Visitors Onsite
In the context of an organization, “visitors” refer to individuals who are not regular employees or members of the organization but enter its premises for a specific purpose or duration. Visitors could include a diverse range of people, such as clients, customers, suppliers, consultants, contractors, job candidates, delivery personnel, or guests attending meetings or events.
These individuals typically have a temporary or intermittent relationship with the organization and may be onsite for various reasons, such as business meetings, interviews, training sessions, or social events. The term “visitor” is broad and encompasses anyone who is not a part of the permanent workforce but has a legitimate reason to be present on the organization’s premises.
Workplace threats are various site security risks that can result in physical harm, financial losses, damage to reputation, and legal liabilities for businesses. These risks necessitate robust security measures incorporated into the visitor management system, including access control systems, surveillance, cybersecurity protocols, and employee training, to protect employees, assets, and sensitive information, ensuring business continuity and regulatory compliance.
For instance, with regard to the food sector, the Food and Drug Administration’s regulation 21 CFR Part 121 Mitigation Strategies to Protect Food Against Intentional Adulteration refers to food defense as the effort to protect food from intentional acts of adulteration where there is an intent to cause wide-scale public health harm. The responsible team has to review and verify the visitor policy as part of the food defense strategy to ensure all visitors understand your basic food defense program, bring efficient visitor movement and access management, and supervise visitor check-in and check-out procedures.
Hence, recognizing the potential risks linked to the presence of visitors in a company’s working environment, grasping their prevalence, and remaining vigilant about them through safe visitor solutions is of paramount importance for uncompromised site security. Let us delve into the various site security and visitor risks.
Unauthorized Access & Unaccounted Visitors
One of the primary concerns when it comes to workplace security is unauthorized access. This occurs when individuals, whether outsiders or employees, gain access to areas they are not explicitly permitted to enter. This threat is often underestimated, as many are unaware of how easily outsiders can enter a building undetected. Unauthorized access can result from well-intentioned employees holding doors for others, accidentally leaving doors unlocked, or even the misuse of key cards. Regardless of the cause, unauthorized access poses a significant risk, as it can lead to data breaches and other security breaches.
A visitor management system in place systematizes workplace operations and strictly monitors the work environment to ascertain unidentified individuals do not gain entry to restricted premises or sections. It also retains a detailed record of all onsite visitors, allowing for easy access to visitor and employee data in case of emergencies, as well as delivering real-time notifications and guidance to employees as and when necessary.
Inconsistent Visitor Training
Improving the awareness of employees about potential cyber threats is an important but often neglected aspect of security. In today’s rapidly evolving technological paradigm, data security risks are on the rise, and cybercriminals continually adapt their tactics to outsmart IT practitioners. Unfortunately, many employees receive minimal or no cybersecurity training. As a result, employees may be unaware of data security risks, such as leaving computers unlocked and unattended, which could lead to malware infections. To address this issue, organizations should make regular cybersecurity education a top priority.
Workplace Disruptions
Unannounced visitors can disrupt the workflow and daily operations of an organization. From unexpected meetings to unscheduled tours, uncontrolled access not only distracts employees but can also lead to decreased productivity. A seamless visitor management process ensures that visits are planned, minimizing disruptions and maintaining the efficiency of the workplace.
Security Breaches
One of the most glaring risks associated with uncontrolled visitors is the heightened potential for security breaches. Unauthorized individuals gaining access to restricted areas can compromise sensitive information, intellectual property, and even the safety of employees. A lack of proper identification and vetting processes opens the door to malicious intent, making it essential to establish stringent access controls.
Health and Safety Concerns
In the age of global health crises, the uncontrolled entry of visitors poses a serious health risk. Without proper screening measures, contagious diseases can be easily transmitted within a facility, putting the health and well-being of both visitors and employees at stake. Visitor Management Systems equipped with health screening protocols become indispensable in mitigating these risks.
Theft and Property Damage
Employee theft is a workplace threat that can cost businesses billions of dollars annually. This includes theft resulting from improper disposal of documents, unattended items in personal vehicles, or unauthorized access by outsiders. By utilizing visitor management software, organizations can track the access patterns of individuals, including employees and contractors, which can be particularly useful in identifying potential theft or property damage incidents.
Failing to address workplace security risks can lead to severe consequences for both the business and its workforce. Therefore, it is imperative that everyone prioritizes safety and integrates security measures into their daily work routines.
Compliance and Regulatory Issues
Industries such as healthcare, finance, and government are bound by strict compliance and regulatory standards. Failure to control visitor access and maintain proper documentation can result in severe legal consequences, including fines and sanctions. A robust visitor management system aids in ensuring compliance with industry-specific regulations.
What is a Visitor Management Software?
A visitor policy outlines a set of regulations specifying who is permitted to enter the premises, the authorized time frames for their presence, and the specific areas within the workplace they are granted access. Adhering to the visitor policy elevates workplace security necessary for safeguarding employees, physical premises, and the business’s essential data and information, all while complying with applicable security laws and regulations.
Visitor management software is a tech-assisted solution used in organizations to establish and enforce their visitor policies by streamlining and enhancing the process of managing visitors to a physical location, such as an office, campus, or facility. The benefits of visitor management software become pivotal in visitor risk mitigation.
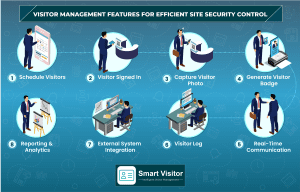
Must-have Visitor Management Features for Efficient Site Security Control
The features of visitor management software are indispensable components of site security control systems. They bring efficacy, accuracy, and proactive monitoring to the forefront, helping organizations defend their premises and resources in an ever-changing security scenario. The following are the must-have features to look for in a visitor management solution for attaining the best outcome for successful site security control.
Visitor Sign-In System
A visitor sign-in system automates the check-in and check-out processes and enables the capture of mandatory visitor information, including names, contact details, and the purpose of the visit. This data is stored securely and can be quickly accessed when needed. It also helps in screening and identifying visitors by integrating with various databases, watchlists, or even facial recognition systems.
It helps regulate and streamline the entry of visitors into a workplace, ensuring adherence to security protocols and visitor policies. Placing a visitor sign-in system in the reception or entry area provides visitors with guidance on the information they need to provide and directions to their destinations. Geofencing capabilities automate the check-in and check-out processes for regular visitors.
Visitors can check in using self-service kiosks as well as print visitor badges using the visitor sign-in system to upgrade workplace compliance. The system should identify and categorize visitors into different types as the visitor sign-in system is applicable not just for occasional external guests but also for employees who come to offices on a regular basis.
Visitor Photo Capture
Visitor Photo Capture significantly enhances security by providing a visual record of each visitor, which serves as a powerful tool in the identification of individuals, making it considerably easier to recognize them in the case of security breaches. By associating a visitor’s face with their provided information, it ensures a clear link between the individual and their visit. In the event of an incident or an inquiry, this feature offers an indisputable record of who was present and when. This not only simplifies incident investigations but also reinforces transparency and responsibility among staff and visitors while improving accountability within an organization.
Receptionists and security personnel can visually compare and verify visitors’ appearances with their captured photos during the check-in process. It serves as an additional identifier in the visitor log, making it easier to retrieve historical data on past visitors. Furthermore, it acts as a deterrent to potential threats as unauthorized individuals contemplating access are aware that their photos will be captured, thus discouraging any malicious intent. This increased level of security instills confidence in both staff and visitors, further solidifying the integrity of the facility.
For organizations operating in regulated industries such as healthcare or finance, having a photographic record of visitors is often a requirement for compliance with security and privacy regulations. This feature provides a clear and indisputable documentation trail that can be invaluable during audits and for legal purposes.
Visitor Badge
A visitor badge is a key element of a visitor access control system that employs ID badge cards to identify and verify individuals seeking entry to specific locations or resources. These badges typically incorporate information such as a photo, name, or unique identification number, along with mechanisms for user authentication using electronic badge readers.
Commonly used technologies for access badges include proximity card access control, RFID, and magnetic stripe technology. RFID badges emit a radio signal read by an antenna at the card reader, offering contactless access within a certain range. Swipe badges utilize a unique magnetic stripe on the card, requiring manual swiping for access. Some organizations are adopting mobile access control ID cards, which are digitally stored within an access app. This eliminates the need for physical ID badge cards.
Considering the inclusion of a visitor badge system into site security management serves as a visitor risk mitigation strategy by preventing unauthorized entry through the deactivation of lost or stolen badges, improving visibility into employee attendance, eliminating manual visitor management and record-keeping procedures, and enabling multiple entry points with a single badge to simplify access control.
Visitor Scheduling
Scheduling visits enables organizations to plan and control visitor access in advance by pre-registering visitors and specifying the date, time, and purpose of their visit. By doing so, organizations can proactively screen visitors and ensure that only authorized individuals gain access to their premises. When visitors arrive at the facility, their pre-scheduled appointments allow for quicker processing and reduce wait times at the reception.
Visitor scheduling in visitor management solutions often allows for on-the-fly scheduling changes, accommodating unforeseen adjustments in visitor plans. Whether a meeting needs to be rescheduled or additional visitors are expected, this feature guarantees that the visitor management system remains agile and responsive to evolving needs.
This feature improves efficiency in visitor management procedures and resource allocation such that offices can allocate resources, such as meeting rooms or parking spaces, more effectively, ensuring that visitor needs are met promptly. Organizations can also optimize staff schedules and plan for visitor arrivals, reducing the strain on administrative personnel and minimizing last-minute disruptions for the staff to allocate their time and attention efficiently, enhancing productivity.
Visitor Log
A visitor log, an integral component of a visitor management system, functions as a meticulous record-keeping tool that documents visitors’ details, their affiliations, the purpose of their visits, contact information, and timestamps for entry and exit.
Conventionally, paper-based logs, often found at front desk receptions, require visitors to manually complete forms with their details, entry times, and the individuals they intend to meet. These tedious logs evolved over time to result in digital logs to organize and automate data entry. They incorporate various features such as QR code-based check-ins, ID card scanning, and even biometric fingerprint verification. They can also identify and restrict entry for blacklisted or unauthorized visitors, monitor visitor durations, and provide access to relevant staff.
Digital visitor logbook systems offer convenience and save time in retrieving data from them by eliminating the need to sift through numerous pages of paper-based visitor records. These, being cloud-based, excel in data security by preserving visitor information from unauthorized access. They can be a treasure trove of data about inbound and outbound visitors, levying a data-driven approach empowering businesses to analyze visitor patterns and make informed decisions with respect to site security systems.
Deploying a visitor log within a visitor management system tends to remediate visitor risks by verifying the credentials of individuals seeking entry to prevent unaccounted visitors from entering the workplace and aiding in providing a one-stop database of information about visitors’ identities and their intended destinations within the facility so that evacuations can be carried out swiftly in case of emergencies or natural disasters.
External System Integration
External system integration is a functionality that provides a seamless connection between the visitor management system and other crucial systems, applications, and databases existing in the enterprise. Examples of such integrations include access control systems, credential checks, emergency response, ID scanning and blocklists, secure WiFi, and background checks, presenting as a stronghold for enhanced site security.
Many organizations have detailed databases containing employee information, security clearances, and access permissions. The integration with systems such as employee directories contributes to managing employee attendance, security, and compliance with office hours. Rather than duplicating data and processes, visitor management software can effortlessly connect with systems such as ID badge printing, email notification, or visitor analytics. This interconnectedness establishes a visitor management system that is fully integrated into the organization’s broader technology ecosystem.
Real-Time Communication
Swift communication tools, such as in-app messaging, email, or SMS, should be integrated into visitor management systems to enable real-time communication between on-site visitors, administrators, and staff.
When a visitor arrives, the host can receive a notification, ensuring a timely and smooth reception. In case of emergencies, such as a fire evacuation or security threat, alerts enable quick dissemination of critical information to all visitors and staff present in the facility, helping ensure their safety. A visitor management system can send automated reminders and confirmation messages to visitors and hosts, reducing no-shows. If there are any security concerns or incidents, rapid communication through the visitor management system can help address them promptly. These systems can also facilitate customized communication, such as providing specific instructions or updates based on the visitor’s purpose or profile.
Reporting & Analytics
Intuitive reporting and analytics tools enable you to utilize the visitor management system for visitor tracking, including visitor history, peak visit times, and security incidents. This information can be invaluable for optimizing site security protocols.
Reporting and analytics capabilities of visitor management software permit establishments to track visitor data, generate reports, and identify visitor trends over time to aid in compliance, visitor flow optimization, and emergency management, equipping modern businesses to transform operational efficiency and the overall visitor experience.
Smart Visitor as an Effective Visitor Management Software
Improve the safety and security of your company’s premises with Smart Visitor, a revolutionary cloud-based solution that automates and centralizes the entire visitor registration and management process, from initial check-in to departure, in a highly customizable and cost-efficient manner. Smart Visitor leverages contactless visitor management technology to offer an exceptional front-office experience, streamlining and enhancing the check-in procedures for visitors at your facility as well as employee sign-in and sign-out management. The features that make Smart Visitor an end-to-end solution for visitor management are:
Configurable Visitor Badge: Customize the visitor badge layout to display essential visitor information as per your preferences by capturing visitor photos and IDs at the entry point for authentication.
Contactless Sign-in: Enable contactless sign-in process via smartphones, generating QR Codes and digital passes for easy check-in and check-out.
Two-Factor Authentication: Ensure security with a two-factor authentication system for signing into the Smart Visitor app.
Guest Pre-Registration: Schedule visits in advance, notifying visitors ahead of time by integrating with email calendars. Store visitor information for returning visitors, allowing one-click sign-ins.
Role-Based Access Control: Assign role-based access to specific areas within your facility, allowing precise control over visitor movement.
Host Alert Notifications: Facilitate effective communication between hosts and visitors through customizable notifications via Email, SMS, and WhatsApp.
Visitor Training: Ensure compliance with health and safety regulations by arranging training for visitors and tracking completion records.
Visitor Agreement: Populate customizable forms with visitor and meeting information to secure visitor agreements with electronic signatures and upload required documents for a systematized visitor data system.
Employee Sign-In/Sign-Out Log: Monitor and manage employee entry and exit with real-time employee logs to gain insight into employee presence and automatically calculate and report employees’ daily working hours.
Third-Party Integration: Smoothly integrate with third-party security or payroll systems for employee working hour calculations.
Multi-Device Support: Access the Smart Visitor app from smartphones, iPads, or desktops via the Android Play Store or iOS App Store.
Reporting: Generate comprehensive reports, including employee analytics, visitor data, and meeting information, using an active dashboard and customizable reports.